In a previous blog post (Better
HA on de RDCB) I wrote a quick feature highlight of the new High Availability options for RD Connection Broker on Windows Server 8 (Beta). I promised to write a more detailed blog post on how to actually set this up. So here it is!
The process for setting up a highly available (HA) RD Connection Broker has changed and improved a lot in Windows Server 8 (Beta). As also seen in my previous blog post on this, a wizard has been added to the new server manager to guide you through the process of setting up the HA and adding new RD Connection Broker servers.
Prerequisites
Before we start to configuration, I’ll quickly sum up the prerequisites. At this point we assume that there is a RD Connection Broker already in place (e.g. during the setup of a quick deployment). The prerequisites for High Availibility for the RD Connection Broker are:
• A Microsoft SQL Server with write permissions granted to all RD Connection Broker servers that will be part of the deployment
• The Microsoft SQL Server Native Client is installed on all RD Connection Broker servers that will be part of the deployment
• Static IP addresses have been assigned to all RD Connection Broker servers that will be part of the deployment
• DNS resource records with a single DNS name have been created for all RD Connection Broker servers that will be part of the deployment
Step 1. Preparing the Broker for HA
Before adding a second server with the RD Connection Broker role we need to prepare the current RD Connection Broker for HA. Which means that during this process, the wizard will create a central database on a central MS SQL Server instance and will transfer the configuration to this database.
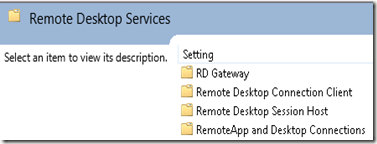
We open the Server Manager on the machine that is currently holding the RD Connection Broker Role and we navigate to “Remote Desktop Services” and then “Overview”. We right-click the RD Connection Broker and choose “Configure RD Connection Broker for HA”.
On the "before you begin" screen the previously discussed prerequisites are summed again, we press “Next”. On the “Configure High Availability” screen we enter the details of the HA setup.
We need to specify the following parameters:
Database connection string
The wizard will use this string to create the database. Pay close attention to the format of the string. Copy the string below and change only replace the <name of SQL server> and <name of database> values.
DRIVER=SQL Server Native Client 10.0;SERVER=<name of SQL server>;Trusted_Connection=Yes;APP=Remote Desktop Services Connection Broker;Database=<name of database>
Folder to store databasefile
Here we need to specify the folder on the SQL Server where we want the databases to be stored. For demo purposes I placed in C:\RCDB, but in most environments you will probably use an existing HA SQL environment and enter the desired values. Note that we specify the location for the .mdf as well as the .ldf file, so no separation there. However, you should be able to change that in using SQL Server manager after the installation.
DNS Resource Record name
Here we specify the DNS name that we want this HA RD Connection broker farm be accessible on. For this demo I used rdcb.lab.local
We click “Next” and click “Configure” on the confirmation page. Shortly after that we get the confirm that the configuration has succeeded.
A database is created on the SQL Server we specified.
Remember that this was just step 1. We now have prepared the current RD Connection Broker for HA purposes.
Step 2. Adding a RD Connection Broker
As the next step we will add a new RD Connection Broker to the HA setup we just created.
We go back to the server manager and we now have the option available “Add Connection Broker Server”.
After clicking next on the prerequisites page we are presented with the screen below. We select the server that we want to add as a RD Connection Broker and click next. (Please remember that before we are able to add a server here that server must be added to the Server Manager to be able for it to configure it).
We click “Add” on the confirm dialog and the wizard will remotely install the RD Connection Broker on the server we selected and add it to HA environment.
And that’s it!
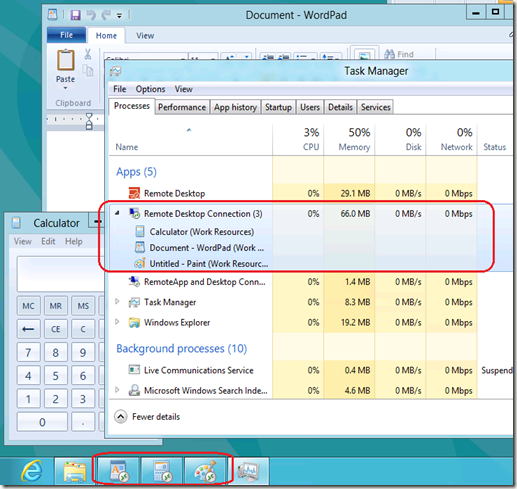
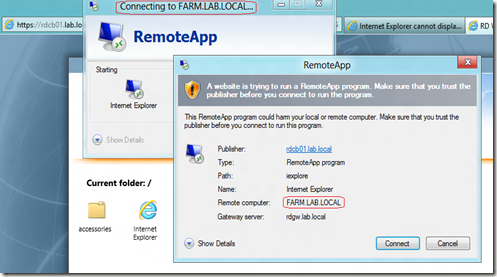
We are now able to remotely connect to the DNS farm name (rdcb.lab.local) we created by using mstsc. An initial connection (
as seen here) will be hosted by one of the active RD Connection Broker servers and we get be redirected to one of the RD Session Host Servers in the Session Collection! (And of course this also works in conjunction with the RD Gateway and RD Web Access).
Conclusion
Windows Server 8 (Beta) supports a true active-active HA solutions for the RD Connection Broker Big improvement !